Go back to the logs directory c program files checkpoint cpuepm rxx logs and collect the entire logs folder and send it to check point support endpoint security engineer.
Heat endpoint security logs.
In case of installation or removal issues in kaspersky endpoint security 11 for windows technical support engineer may ask you to send an installation or removal log file for troubleshooting.
If you have not already created the endpoint for cloudwatch logs choose create endpoint.
Where to find the log files.
C documents and settings all users application data checkpoint endpoint security logs uploaded according to the common client policy to the endpoint security management server and viewable in the logs tab of the smartconsole logs monitor view.
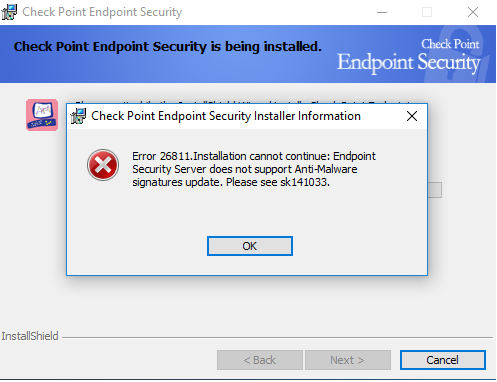
This solution has been verified for the specific scenario described by the combination of product version and symptoms.
Endpoint protection in sccm allows you to manage anti malware policies and windows firewall security for client computers in your configuration manager hierarchy.
Folders found on disk after you uninstall heat endpoint security client from your pc.
The log file sms dm log on the site system server also records communication between mac computers and the management point that is set up for mobile devices and mac computers.
Heat emss 8 4 focuses on the features and usability requirements most requested by our customers said david murray product manager at heat software.
Here is table that lists sccm endpoint protection log files and location of each log file.
Then select com amazonaws region logs and choose create endpoint.
Log files are generated automatically and stored in the temp folder.
The following sections list log files that are on the site server or that are related to specific site system roles.
Choose edit policy and make the changes to the policy.
Some files and registry entries are usually left behind when you remove heat endpoint security client.
C program files heat software endpoint security client.
Client logs can be used for external audit requirements and internal trouble shooting.
Select the com amazonaws region logs endpoint and choose the policy tab in the lower half of the screen.
The suite provides defense in depth endpoint security simplified endpoint management and reduced endpoint total cost of ownership while offering added protection against targeted attacks.